ZipIPS™: Quantum-Secure IoT Authentication with NanoTimestamp Power
The Core Idea
Most security systems protect a secret — a key, a password, something static that gets used over and over. The attacker's job is to find that secret. Once they have it, they're in forever.
ZipIPS™ doesn't work that way.
Heraclitus had the right idea — you can't step into the same river twice. Every instant is unique, just like every timestamp is unique, and that powerful idea can be used to secure networks no matter how fast quantum computers can guess.
Every timestamp is unpredictably different, down to the nanosecond if your system can generate nanosecond precision — as the U.S. Naval Observatory does for timekeeping standards. Or down to the microsecond, or the millisecond — whatever your system clock supports. The patents were written based on millisecond precision and already exceed NIST post-quantum and lightweight cryptography standards. Nanosecond precision only makes ZipIPS™ more powerful. The architecture scales with your hardware — the more precise your clock, the stronger your authentication.
Every authentication credential is tied to a single, unrepeatable and unpredictable timestamp. Both devices independently derive the credential from pre-shared tables that never cross the network. There is no static key to steal. No credential to replay. Authentication works both ways — the client verifies the host and the host verifies the client, each generating a fresh timestamp and independently confirming the response before access proceeds. Any device can challenge the commanding host before executing a new instruction — blocking man-in-the-middle attacks before they start. Failed attempts are immediately blocked, permanently logged, and available for review.
This is Zero Trust at the device level: never trust, always verify.
How It Works
Both the requesting device (client) and the receiving device (host) hold identical copies of two types of tables — provisioned before any session begins and never transmitted during operation:
- String tables: For every possible value of each time unit, there is a randomly generated character string. The patent allows strings of any length and any character set — the more complex, the higher the security. There is no upper limit.
- Sequence tables: For each possible millisecond value (000 through 999), there is a unique random ordering of the time units. This determines the order in which strings are assembled into the credential — and it is never transmitted. Both devices derive it independently from the timestamp. An attacker watching the network sees a credential but has no idea what strings are in it or what order they are in. There is nothing to work backwards from.
Every lookup table contains exactly 1,000 entries regardless of how many values the time unit actually uses — so an attacker who gains access to a table's structure cannot determine which time unit it represents just by counting rows.
The Double Two-Way Handshake
ZipIPS™ authentication does not trust a single exchange. Both devices must independently verify each other across two complete cycles before any session proceeds. No clock synchronization is required — each device uses its own internal clock, and the timestamp itself travels with the credential as the lookup key:
- The client generates a first timestamp, assembles a credential from its host string table in sequence-determined order, and sends both the timestamp and credential to the host.
- The host uses the provided timestamp as the lookup key and independently derives the same credential from its own identical tables — no clock synchronization needed. It compares its independently derived credential to the one received. If they match, the host generates a second timestamp — one the client has never seen and could not have predicted — and sends it back as a new challenge.
- The client uses the new, unpredictable timestamp as its lookup key and must respond with the correct credential from its private client tables. Only a device that actually has the right tables can answer correctly — every time, for any timestamp, no matter how unpredictable.
- On demand, any device can generate a further unpredictable timestamp challenge to re-verify the commanding host before executing a new instruction. A substituted or hijacked host cannot produce what it doesn't have.
Key Properties
| Property | What It Means |
|---|---|
| No static credential | Every exchange generates a unique credential tied to a single, unrepeatable and unpredictable timestamp. There is nothing persistent to steal, capture, or replay. |
| No transmitted sequence | The sequence ordering that makes each credential unique is derived independently by both devices — it never crosses the network. An intercepted credential reveals nothing about the next one. |
| No clock synchronization required | Each device uses its own internal clock. No synchronized time infrastructure is required — eliminating a known attack surface and enabling authentication in degraded or denied communications environments. |
| Quantum-secure by construction | ZipIPS™ does not rely on mathematical hardness assumptions that quantum computing threatens — no RSA, no ECC, no discrete logarithm. Security derives from timestamp resolution and table complexity. Quantum algorithms have no structure to attack. |
| Double two-way handshake | Both devices verify each other independently. Neither side grants access on a single exchange. Mutual authentication is required before any session proceeds. |
| On-demand generation only | Credentials are generated only when an authentication event occurs. No background process, no idle computation — critical for power-constrained IoT devices. |
| Permanent audit log | Every authentication attempt — successful or failed — is permanently logged and available for review. A complete, tamper-evident record of every exchange. |
| Zero Trust at device level | Implements NIST SP 800-207 Zero Trust principles — never trust, always verify — at the device authentication layer. No prior session, no network position, no cached credential grants access. |
Security Performance
ZipIPS™ is a licensable architecture — licensees write their own implementation code and configure the system for their specific environment. The following illustrative entropy levels represent what the architecture can achieve. There is no upper limit — licensees can increase entropy by adding character sets, time units, or any real-time data their systems can generate on demand.
| Implementation | Entropy | Payload Size | Characteristics |
|---|---|---|---|
| ms original | 381 bits | 95 bytes | Millisecond-resolution timestamps. Alphanumeric character strings. Eight time units. |
| ns standard | 476 bits | 117 bytes | Nanosecond-resolution timestamps. Alphanumeric character strings. Ten time units. |
| ns+ high security | 735 bits | 157 bytes | Maximum time-unit depth with non-control special characters from the extended ASCII character set. |
NIST Security Level Comparison: Bits of Security
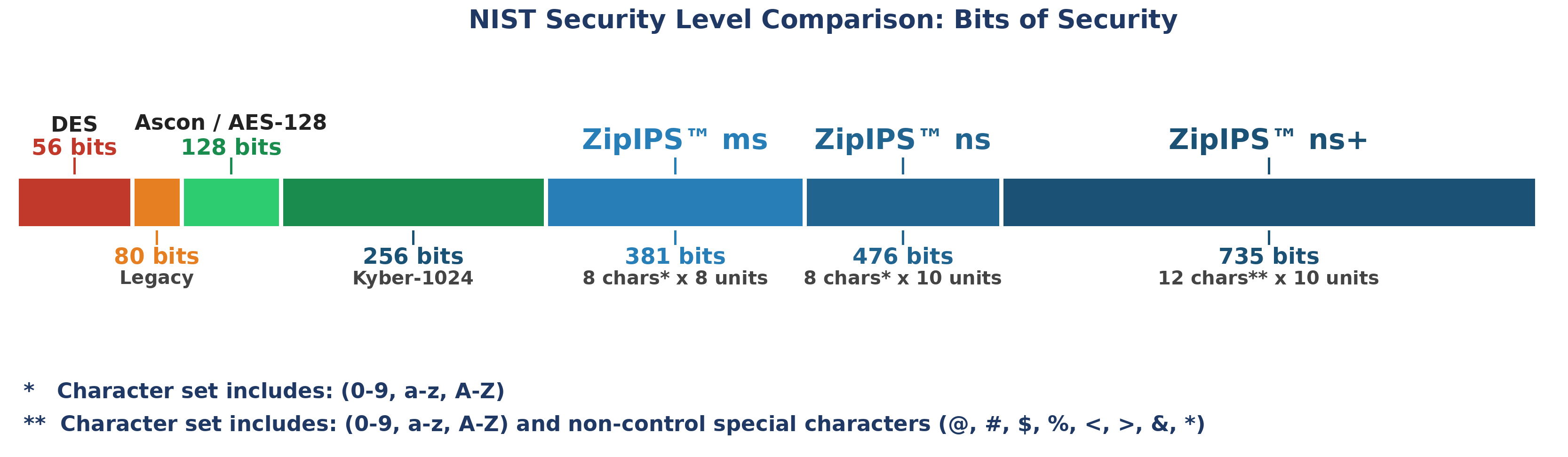
ZipIPS™ ms (381 bits) · ns (476 bits) · ns+ (735 bits) — compared to DES, AES-128, and CRYSTALS-Kyber-1024. Click to enlarge.
Credential Size Comparison: Bytes per Authentication
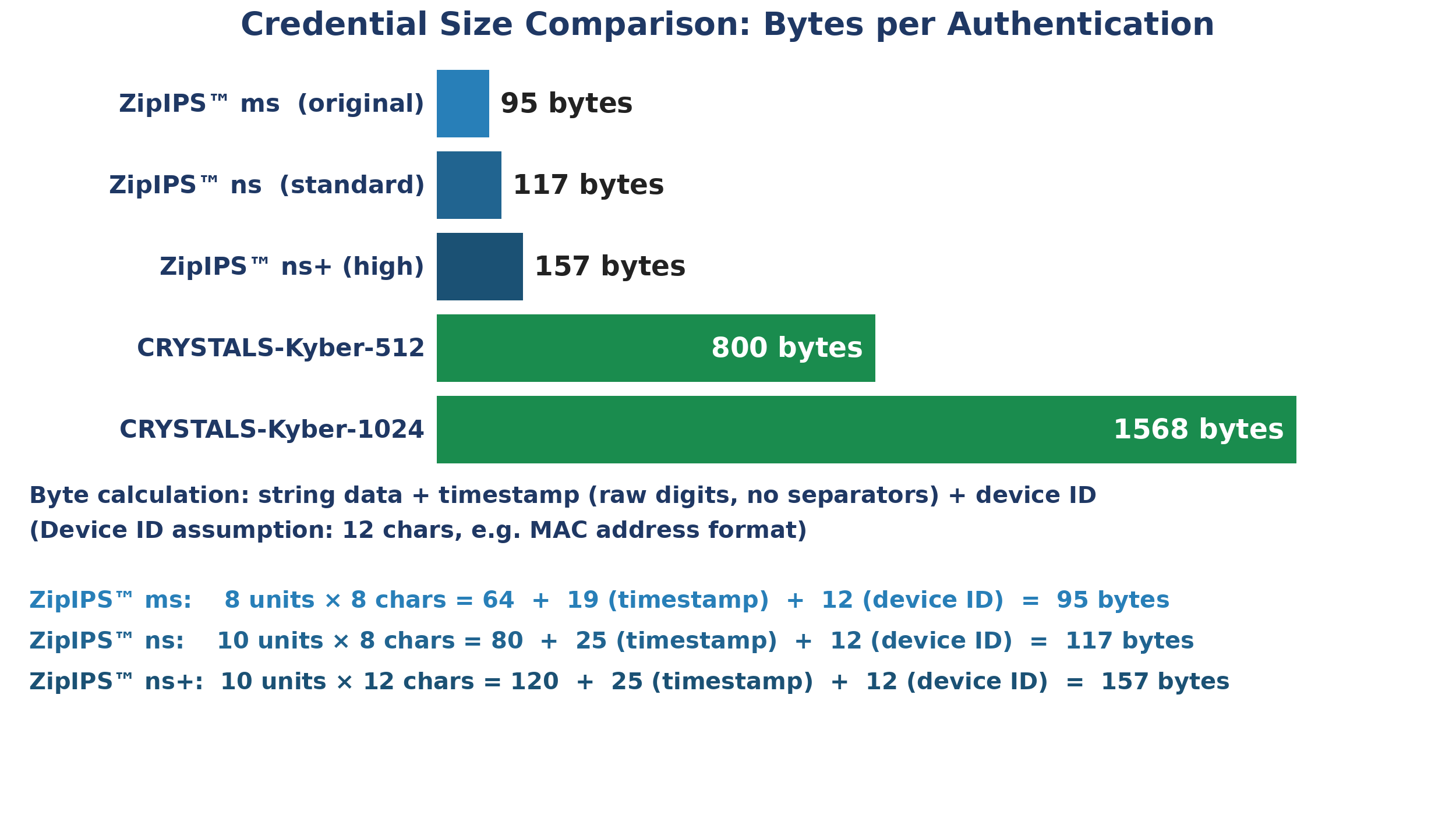
ZipIPS™ credentials (95–157 bytes) vs. CRYSTALS-Kyber-512 (800 bytes) and Kyber-1024 (1,568 bytes). Click to enlarge.
For Cybersecurity Professionals
ZipIPS™ operates at the device authentication layer — the foundation beneath the security stack that tools like SIEM, IDS, and endpoint detection systems depend on. If the authentication layer is compromised, no amount of monitoring above it makes the system secure. ZipIPS™ hardens that foundation.
In Zero Trust architecture terms (NIST SP 800-207), ZipIPS™ implements the core principle at the device level: every session is independently challenged, every command is verified before execution, and no device is trusted based on prior authentication or network position. The permanent, tamper-evident audit log provides the verifiable record that compliance frameworks require.
For cybersecurity firms advising clients across multiple verticals, ZipIPS™ is a horizontal capability — the same patented architecture applies to banking infrastructure, industrial control systems, autonomous vehicles, defense systems, healthcare IoT, and Agentic AI command channels. One licensing conversation covers every vertical where device-level authentication matters.
ZipIPS™ credentials function as a nonce — a Number used ONCE — but unlike traditional nonces, the sequence ordering is never transmitted across the network. There is nothing to intercept that would be useful for any future exchange. And because every failed attempt permanently invalidates that timestamp, there is no iterative search possible — AI-assisted brute force attacks have no foothold.
NIST Alignment
| NIST Publication | ZipIPS™ Alignment |
|---|---|
| SP 800-207 (Zero Trust) | ZipIPS™ implements Zero Trust at the device authentication layer — every session independently challenged, every command verified before execution, no implicit trust based on prior session or network position. |
| SP 800-213A (IoT Authentication) | ZipIPS™ provides device-level mutual authentication — both devices verify each other independently through the double two-way handshake, directly addressing IA-3 device authentication requirements. |
| FIPS 203/204/205 (PQC Standards) | ZipIPS™ does not rely on any quantum-vulnerable algorithm. Security derives from timestamp resolution and table complexity — quantum-secure by architecture, not by algorithm selection. |
| SP 800-232 (Lightweight / Ascon) | ZipIPS™ exceeds the Ascon baseline at every implementation level: ms original (381 bits), ns standard (476 bits), ns+ high security (735 bits) — all surpassing Ascon's 128-bit security level. |
| NIST IR 8547 (PQC Transition) | High-risk systems must transition to quantum-safe authentication ahead of 2035. ZipIPS™ is deployable now, on existing device infrastructure, with no cryptographic migration project required. |
Note: These alignments are architectural observations, not certifications. ZipIPS™ has not been submitted to NIST for evaluation or endorsement.
Implementation Platforms
ZipIPS™ is a licensable software architecture — licensees write their own implementation code. The architecture is platform-agnostic and has been analyzed as compatible with the full range of IoT and embedded computing platforms, including microcontrollers, ASICs, CPUs, DSPs, SoCs, and embedded FPGAs (eFPGAs). Implementation requirements vary by environment and are the licensee's responsibility to evaluate.
Patent Foundation
US10348729B2 — System patent. Issued July 9, 2019. Covers the authentication architecture: host device with sequence tables and string tables at variable security levels, client device with mirrored table architecture, device identifier, and the complete double two-way handshake system. Continuation of US10171465B2.
Both patents are assigned to Helene E. Schmidt, Creative Synergies LLC. Prospective licensees are encouraged to review the patents directly and consult qualified patent counsel regarding scope.
Technical Documentation
The following resources provide deeper technical and commercial detail:
The ZipIPS™ Technical Analysis — an independent technical analysis of U.S. Patents US10171465B2 and US10348729B2, written in the direct explanatory style of Richard Feynman — is available upon request. Contact us to receive a copy.
ZipIPS™ is available for licensing. Please explore this site and Contact Us if you have any questions.
